-
-
Notifications
You must be signed in to change notification settings - Fork 234
Group Policy Editor
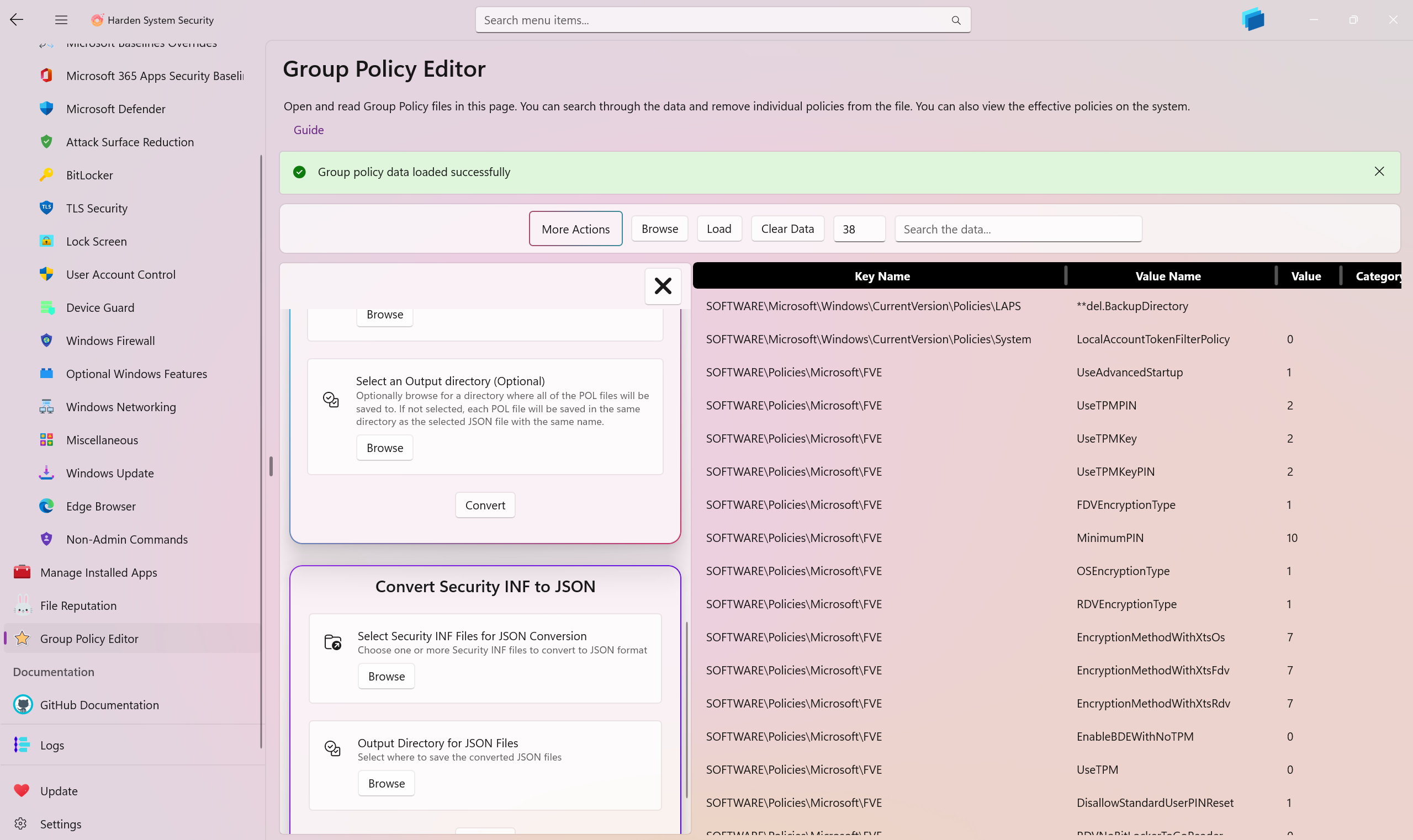
The Group Policy Editor page enables you to retrieve the effective policies on the system. You can sort and search through this data via the available UI controls. You can also browse for .POL group policy files on your system or a shared network location in order to inspect it.
Since the Harden System Security app can be set as the default handler of the .POL files, this page is also displayed when you double-click or tap on any .POL file in the File Explorer.
You may remove any policy from a .POL file — whether a system .POL or one you opened in the app. All edits are correctly persisted back to the selected .POL file.
If you have multiple .POL Group Policy files, you can quickly and accurately merge them into a single .POL file. The result will not have any duplicate policies in it. Select one main .POL file and then select other .POL files you want to merged with the main one. If 2 or more items with the same KeyName and ValueName exist, the ones from the other files will take precedence and overwrite the ones in the main file. This way you can consolidate your group policies without losing any important settings. This logic closely follows other merging strategies used in tools such as LGPO.exe.
You can convert your .POL files into JSON format. The Harden System Security app defines a JSON schema that preserves all of the policy details during conversion. You can reuse and import the same JSON files later in the app.
You can convert the JSON files created by the Harden System Security app back to .POL files in a lossless manner.
Security INF files generated by the Secedit tool can be converted to JSON file format defined by the Harden System Security app. Please keep in mind that only the [Registry Values] section of the INF files are converted to JSON at the moment.
Use this feature to create a very comprehensive security and policy report of the system and export them to a file. The report contains all of the security policies normally generated by Secedit, plus additional information about the current system.
- Create AppControl Policy
- Create Supplemental Policy
- System Information
- Configure Policy Rule Options
- Policy Editor
- Simulation
- Allow New Apps
- Build New Certificate
- Create Policy From Event Logs
- Create Policy From MDE Advanced Hunting
- Create Deny Policy
- Merge App Control Policies
- Deploy App Control Policy
- Get Code Integrity Hashes
- Get Secure Policy Settings
- Update
- Sidebar
- Validate Policies
- View File Certificates
- Microsoft Graph
- Protect
- Microsoft Security Baselines
- Microsoft Security Baselines Overrides
- Microsoft 365 Apps Security Baseline
- Microsoft Defender
- Attack Surface Reduction
- Bitlocker
- Device Guard
- TLS Security
- Lock Screen
- User Account Control
- Windows Firewall
- Optional Windows Features
- Windows Networking
- Miscellaneous Configurations
- Windows Update
- Edge Browser
- Certificate Checking
- Country IP Blocking
- Non Admin Measures
- Group Policy Editor
- Manage Installed Apps
- File Reputation
- Audit Policies
- Cryptographic Bill of Materials
- Introduction
- How To Generate Audit Logs via App Control Policies
- How To Create an App Control Supplemental Policy
- The Strength of Signed App Control Policies
- How To Upload App Control Policies To Intune Using AppControl Manager
- How To Create and Maintain Strict Kernel‐Mode App Control Policy
- How to Create an App Control Deny Policy
- App Control Notes
- How to use Windows Server to Create App Control Code Signing Certificate
- Fast and Automatic Microsoft Recommended Driver Block Rules updates
- App Control policy for BYOVD Kernel mode only protection
- EKUs in App Control for Business Policies
- App Control Rule Levels Comparison and Guide
- Script Enforcement and PowerShell Constrained Language Mode in App Control Policies
- How to Use Microsoft Defender for Endpoint Advanced Hunting With App Control
- App Control Frequently Asked Questions (FAQs)
- System Integrity Policy Transformations | XML to CIP and Back
- About Code Integrity Policy Signing
- Create Bootable USB flash drive with no 3rd party tools
- Event Viewer
- Group Policy
- How to compact your OS and free up extra space
- Hyper V
- Git GitHub Desktop and Mandatory ASLR
- Signed and Verified commits with GitHub desktop
- About TLS, DNS, Encryption and OPSEC concepts
- Things to do when clean installing Windows
- Comparison of security benchmarks
- BitLocker, TPM and Pluton | What Are They and How Do They Work
- How to Detect Changes in User and Local Machine Certificate Stores in Real Time Using PowerShell
- Cloning Personal and Enterprise Repositories Using GitHub Desktop
- Only a Small Portion of The Windows OS Security Apparatus
- Rethinking Trust: Advanced Security Measures for High‐Stakes Systems
- Clean Source principle, Azure and Privileged Access Workstations
- How to Securely Connect to Azure VMs and Use RDP
- Basic PowerShell tricks and notes
- Basic PowerShell tricks and notes Part 2
- Basic PowerShell tricks and notes Part 3
- Basic PowerShell tricks and notes Part 4
- Basic PowerShell tricks and notes Part 5
- How To Access All Stream Outputs From Thread Jobs In PowerShell In Real Time
- PowerShell Best Practices To Follow When Coding
- How To Asynchronously Access All Stream Outputs From Background Jobs In PowerShell
- Powershell Dynamic Parameters and How to Add Them to the Get‐Help Syntax
- RunSpaces In PowerShell
- How To Use Reflection And Prevent Using Internal & Private C# Methods in PowerShell
